The construction industry is finally catching up with digitization, and an increasing number of firms, organizations, and software platforms store their data on the cloud. Which is great!
But as for data security? That’s less great; it’s lagged behind other industries, with 45 percent of construction firms reporting significant leaks of internal information in 2020 alone! (2019/20 Kroll Global Fraud and Risk Report)
 Sebastian Barthelmess
Sebastian BarthelmessSecuring Information in the Construction Industry.
With the right protections in place, a cloud-based platform can actually be more secure than on-site servers and hard drives. They’re also much easier to manage than Virtual Private Networks (VPN), which is good news since remote work is the new standard, despite the grumbling of older generations, and isn’t going anywhere.
So, the importance of securing digital assets is crucial in the AEC industry; so how can you be sure your data is secure when you manage your projects with BIM Track? Let’s talk about it.
1. ISO 27001 Certification
ISO 27001 is an internationally recognized standard for an Information Security Management System (ISMS), and BIM Track is the first issue-tracking platform to be ISO 27001 certified. This certification, which is used by every major software giant including Google, Apple, and Intel, proves that the BIM Track platform, its software engineering processes, and its business operations all value international security standards.
So, what does BIM Track’s ISO 27001 certification mean for clients?
-
Peace of mind.
You can rest assured knowing that BIM Track has been audited and certified by an accredited certification body. -
Protection from third-party risks.
Meeting the ISO 27001 standard helps keep your data secure and free from attack.
-
Protection of your reputation.
In the event of a breach, an ISO 27001-certified partner helps protect your organization.
For a software platform to be truly secure, it’s vital that the organization itself is ISO 27001 certified, and not just the server where the software is hosted. Cybersecurity is like a chain - only as strong as the weakest link.
2. Data Hosting
Some countries have data residency requirements: organizations have to host project data locally, especially in the public sector. So BIM Track hosts your data in different jurisdictions to help you meet your data residency requirements. Our current data hosting regions include Canada, Europe, and the United States.
Choosing your data hosting location is simple when creating a new hub on BIM Track:
Let’s dive deeper into how your data is stored. According to Cisco:

Cisco
What is a data center?

BIM Track customer data is stored in Microsoft Azure data centers, which are ISO/IEC 27001 and SOC 2 Type 2 certified. These data centers have extensive layers of protection: access approval at the facility’s perimeter, inside the building, and on the datacenter floor.
But beyond physical security, BIM Track also relies on Azure services that are top of the line cloud-based data management platforms, and are audited regularly to ensure that they always provide a secure development environment for users like BIM Track.
3. Data Protection
Ok, we’re about to get really technical. Ready?

Data encryption converts electronic data into another form, which makes it difficult to be deciphered by unauthorized parties. It is essential that sensitive information is sent in an encrypted format through Transport Layer Security (TLS) secure protocol, which in the context of a web-based application is called HTTPS. For very sensitive information, it is also a good idea to make sure that the data that is stored at rest, which means, on the data servers’ storage, is encrypted.

BIM Track uses 256-bit advanced encryption (AES-256) transmitted using Transport Layer Security (TLS) to protect your data while it is in transit, which is considered the gold standard in cloud security. BIM Track also protects your stored information using at-rest encryption to ensure your archived data and backups are protected.
Your data is also protected by a robust backup policy with Microsoft Azure, and a recovery plan in case of natural disaster in the main servers’ location.
4. Fine-Tuned Authentication and Access Control
Authorization and access control is an important part of data security. We recommend that BIM Track hub owners regularly review user roles to make sure that only authorized users continue to access your projects.
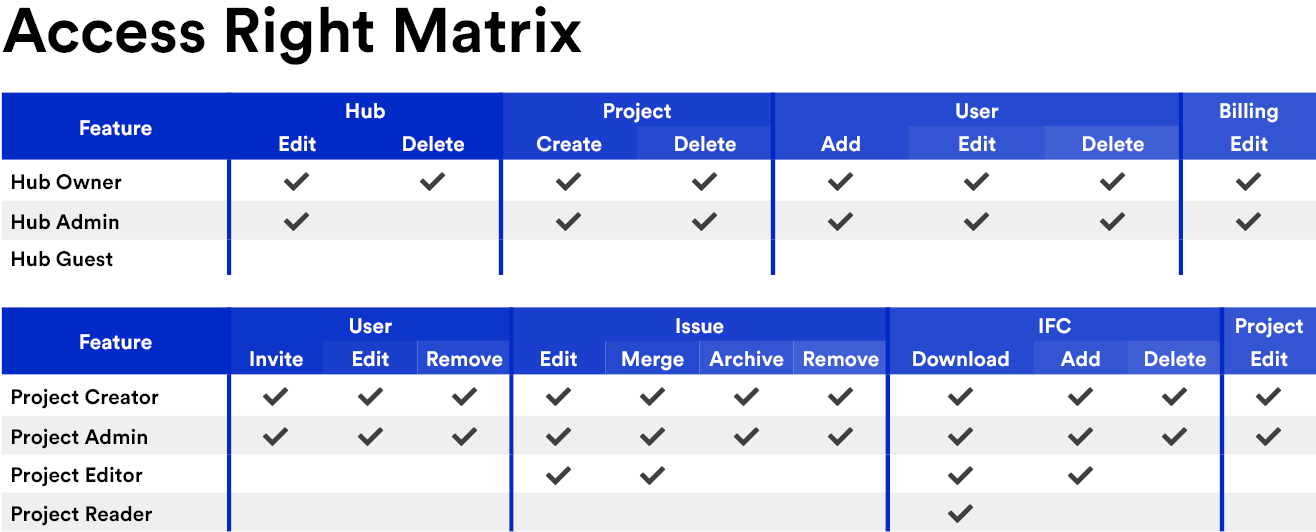
BIM Track gives you the ability to fine-tune access control on the 'Hub Settings' page or the 'Team and Users' page. Here’s an overview of access rights at the hub and project level:
Beyond that, with BIM Track, clients can leverage single sign-on (SSO), allowing them to rely on their own security policy for authentication, including things like generating and managing random and complex passwords, multifactor authentication, and identity monitoring.
5. Secure Development Environment
BIM Track’s developers and product management teams use secure coding practices in accordance with the OWASP standard, the internationally recognized leader in application security.

In a secure development environment, separating the development and test activities from operational environments reduces the risks of inadvertent or unauthorized modifications to the operational system, which could compromise the system's integrity or availability.
At BIM Track, our development, testing, and production environments are separated. Quality Assurance is involved at each phase of the lifecycle. We regularly perform vulnerability scanning, as well as regression testing and penetration testing. Finally, all changes are peer reviewed and logged prior to deployment into the production environment.
6. Strong Security Culture
As well as the technical details, we focus on the human side of data security by building a strong security culture at BIM Track. Our #SecurityCulture includes a comprehensive security policy, ongoing security awareness training, an internal InfoSec helpline, and a commitment to continual improvement.
The bottom line is, we care about security as much as our clients do, and we keep our software on the cutting edge of security standards. Do you have security concerns for your organization’s data? Do you have questions about how your organization’s data can be more securely managed? Feel free to reach out to our dedicated security team at security@bimtrack.co. Trust me, they love to talk shop about this kind thing!

